Blog
Cybersecurity Blogs
Practical articles, guidance, and expert analysis for security teams and business decision-makers.
Blog
Latest Blog Articles
 Blog
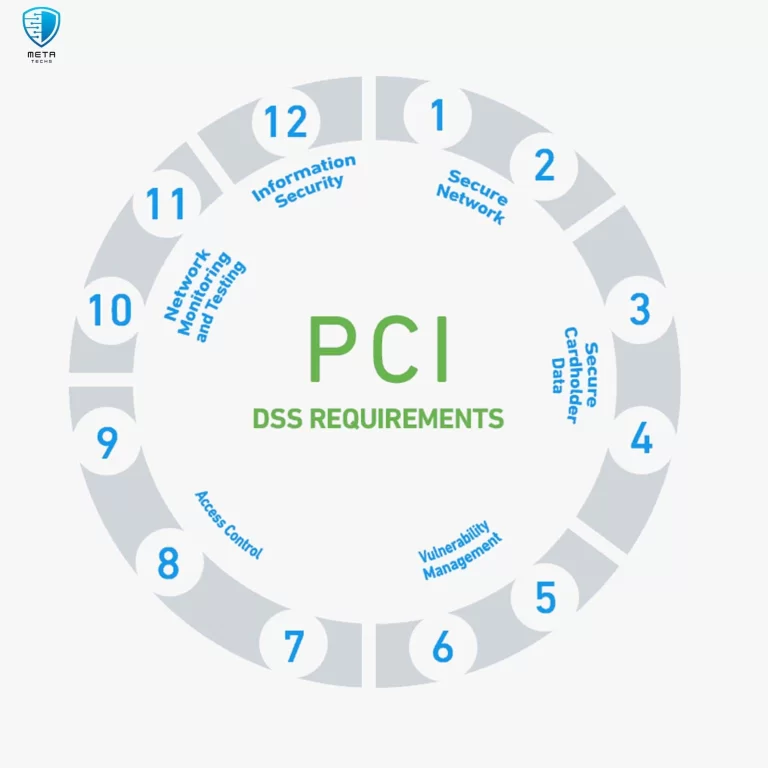
BlogWhat are the 12 requirements of pci dss compliance?
12 requirements of pci dss stands for Payment Card Industry Data Security Standard. It’s a set of security standards designed to protect…Read Blog Blog
BlogIvanti CSA Vulnerabilities in Active Exploitation
Ivanti CSA is a widely used IT service management tool that helps organizations automate and streamline IT processes. However, the recently discovered…Read Blog Blog
Blog3 Critical CVEs in Palo Alto Networks Expedition
Palo Alto Networks Expedition is a powerful network security tool that plays a critical role in protecting organizations from cyber threats. It…Read Blog Blog
BlogCritical Vulnerabilities in GitHub Enterprise Server
The Importance of GitHub Enterprise Server GitHub Enterprise Server (GHES) is a powerful collaboration platform that plays a crucial role in modern…Read Blog Blog
BlogTop 10 Fortinet Firewall Distributor in UAE
Fortinet Firewall Distributor has established itself as a leading provider of network security solutions, offering a comprehensive suite of products to safeguard…Read Blog Blog
BlogHookChain: A New Threat to Bypass EDR
In today’s digital landscape, organizations face an ever-evolving threat landscape, with cyberattacks becoming increasingly sophisticated and mysterious. EDR and XDR solutions have…Read Blog Blog
Blog5 Top GRC Companies In Dubai
Top GRC Companies In Dubai. In today’s rapidly evolving business environment, characterized by increasing regulatory complexity, emerging risks, and heightened stakeholder expectations,…Read Blog Blog
BlogA Comprehensive Guide for Essential VMware Tools
VMware Tools is a leading provider of virtualization solutions, empowering organizations to optimize their IT infrastructure and enhance operational efficiency. Virtualization technology…Read Blog Blog
Blog