Blog
Cybersecurity Blogs
Practical articles, guidance, and expert analysis for security teams and business decision-makers.
Blog
Latest Blog Articles
 Blog
BlogMaster IT Auditing with a Certified Information Systems Auditor (CISA) Certification
In today’s digital age, organizations increasingly rely on information systems to drive business operations, make informed decisions, and maintain competitive advantage. As…Read Blog Blog
BlogYour Guide to ITIL 4 Foundation Training
ITIL (Information Technology Infrastructure Library) is a widely recognized framework that provides a set of best practices for ITSM. ITIL 4 Foundation…Read Blog Blog
BlogHackers leak documents from Pentagon IT services provider Leidos
The recent cyberattack on Leidos, a major Hackers leak documents from Pentagon IT services provider Leidos, has sent shivers down the spines…Read Blog Blog
BlogWhat are the 5 Key Principles of Cyber Security?
In today’s digitally interconnected world, cybersecurity has become an indispensable component of protecting individuals, organizations, and critical infrastructure from cyber threats. cybersecurity…Read Blog Blog
BlogWhat happened with the Windows outage?
On July 18th, 2024, a seemingly routine security update from cybersecurity firm CrowdStrike triggered a global IT nightmare. The culprit behind the…Read Blog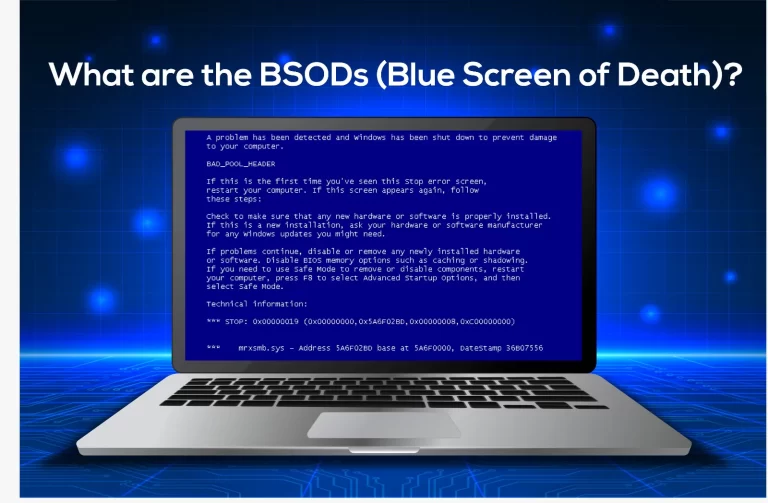 Blog
BlogWhat are the BSODs (Blue Screen of Death)?
The sight of a blue screen plastered across your computer monitor can be enough to send shivers down any user’s spine. Often…Read Blog Blog
BlogWhat is the difference between VAPT and Pentest?
Cybersecurity is paramount in today’s digital world, where businesses and individuals rely heavily on technology. It’s the practice of protecting our data,…Read Blog Blog
BlogWhat is CISSP Certification? Importance and Requirements
The digital landscape is full of security threats. That is why organizations require skilled professionals to safeguard their data. Earning the Certified…Read Blog Blog
Blog