Blog
Cybersecurity Blogs
Practical articles, guidance, and expert analysis for security teams and business decision-makers.
Blog
Latest Blog Articles
 Blog
Blog10 best network security monitoring tools 2024
As technology continues to advance and our lives become more digital, the need for network security monitoring tools has never been more critical.…Read Blog Blog
BlogPalo alto vulnerability cve 2024 3400 Discovery
CVE-2024-3400, recently came to light, affecting the widely used Palo Alto Networks PAN-OS software for specific versions and configurations. This critical flaw,…Read Blog Blog
BlogVeeam Service Provider Console CVE-2024-29212 Vulnerability
Veeam, a top provider of backup and data protection solutions, has issued an important security alert regarding a remote code execution (CVE-2024-29212)…Read Blog Blog
BlogThe Power of cybersecurity and threat management
cybersecurity and threat management cannot be overstated. As we delve into the complex world of protecting digital assets, understanding the nuances of…Read Blog Blog
BlogWhat Exactly is the definition of dark web?
The dark web or the definition of dark web refers to the encrypted portion of the internet that is not visible to…Read Blog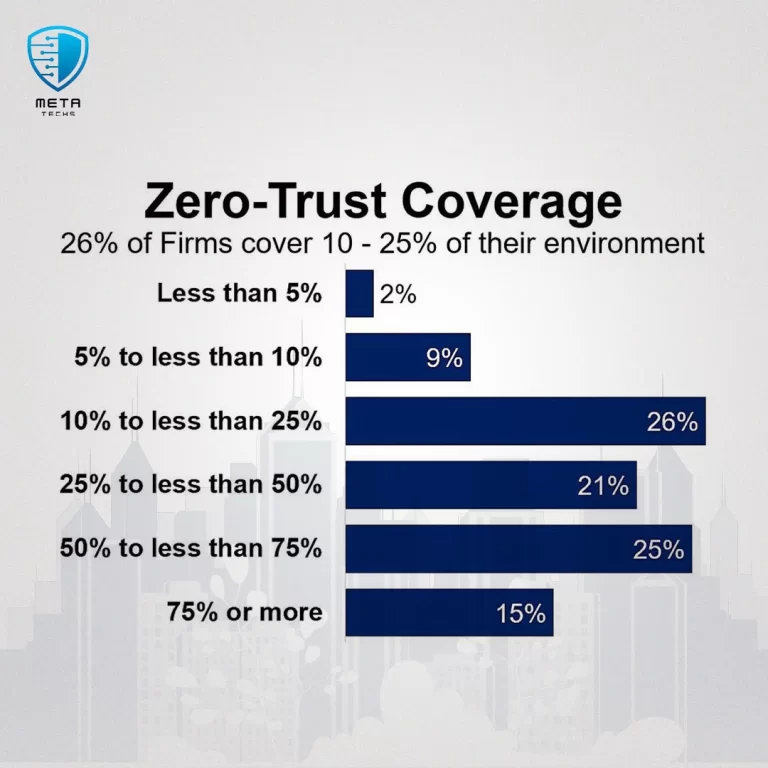 Blog
BlogImplementation Guide to dod zero trust strategy
The Department of Defense (DoD) has released a dod zero trust strategy aimed at achieving an enterprise-wide zero trust cybersecurity framework by…Read Blog Blog
Blogwhat is the main purpose of cyberwarfare?
Ever asked yourself what is the main purpose of cyberwarfare? the threat of cyber-attacks looms larger than ever, marking the rise of…Read Blog Blog
Blog7 Reasons why you need managed it services
We’ve become increasingly to know why you need managed it services as its reliant on technology to run our businesses smoothly and…Read Blog Blog
Blog