Blog
Cybersecurity Blogs
Practical articles, guidance, and expert analysis for security teams and business decision-makers.
Blog
Latest Blog Articles
 Blog
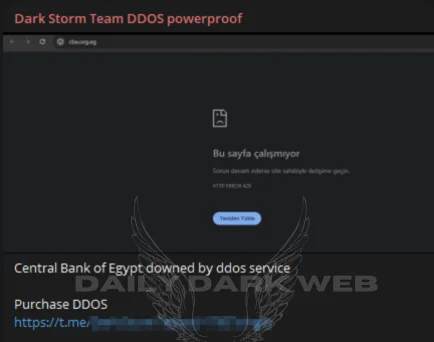
BlogDark storm attack central bank of egypt
In a shocking turn of events, the Central Bank of Egypt fell victim to a massive Distributed Denial of Service (DDoS) attack…Read Blog Blog
BlogBoost Your Business with Top cybersecurity consulting in dubai
Meta Techs cybersecurity consulting in dubai reigns as one of the leading cybersecurity consultant companies in Dubai, leveraging its expertise and cutting-edge…Read Blog Blog
Blogwhy do we need penetration testing
Most of companies ask why we need penetration testing, Vulnerability Assessment and Penetration Testing has become a top priority for companies of…Read Blog Blog
BlogNew attack vectors in EKS
New attack vectors in EKS have emerged, posing potential risks to cloud security. In this article, we will explore these New attack…Read Blog Blog
BlogRansomware attack hits dozens of Romanian hospitals
In a shocking turn of events, Ransomware attack hits dozens of Romanian hospitals. This cyber assault has left the country’s healthcare system…Read Blog Blog
BlogAll you need to know about deepfake cfo hong kong
The world of finance was shaken when news broke of a staggering $25.6 million USD fraud case involving a deepfake cfo hong…Read Blog Blog
BlogThe Truth about the smart toothbrush ddos attack
The story broke when a Swiss newspaper, Aargauer Zeitung, reported that hackers had hijacked approximately three million smart toothbrush ddos attack to…Read Blog Blog
BlogCybersecurity Third Party Risk Management
cybersecurity third party risk management refer to the potential vulnerabilities and threats that arise when an organization shares access to its internal…Read Blog Blog
Blog