In today’s digital world, vast amounts of information are publicly available online, and this data can be both valuable and dangerous. Cybersecurity professionals, investigators, and even attackers rely on structured methods to collect and analyze this information. This is where the OSINT framework plays a critical role.
An OSINT framework helps organize the process of gathering open-source intelligence in a structured, ethical, and efficient way. It allows organizations to understand their digital exposure, identify risks, and improve overall security awareness.
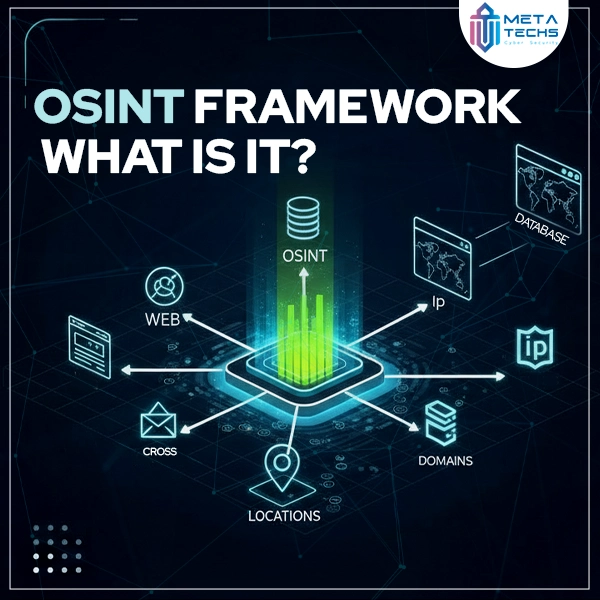
OSINT Framework: What Is It?
An OSINT framework is a structured approach used to collect, organize, and analyze information from publicly available sources. Instead of randomly searching the internet, the OSINT framework provides a clear methodology and categorized resources for intelligence gathering.
The OSINT framework helps users:
- Identify relevant public data sources
- Collect information legally and ethically
- Analyze data to uncover risks or insights
- Turn public data into actionable intelligence
It is widely used in cybersecurity, threat intelligence, digital investigations, and risk assessment.
Read More : What Is OSINT (Open-Source Intelligence)?
Open-Source Intelligence Tools
The OSINT framework relies on a wide range of open-source intelligence tools that collect data from public platforms. These tools help automate and simplify the intelligence-gathering process.
Common OSINT tools include:
- Search engines and advanced search operators
- Social media analysis tools
- Domain and IP lookup tools
- Email and username investigation tools
- Metadata and document analysis tools
By organizing these tools into categories, the OSINT framework allows users to choose the right tool based on their investigation goals.
What Are the 5 Steps of OSINT?
A well-structured OSINT framework typically follows five key steps:
- Planning
Define the objective and scope of the intelligence gathering process. - Data Collection
Gather information from publicly available sources such as websites, social media, and public databases. - Data Processing
Filter, organize, and clean the collected data to remove irrelevant information. - Analysis
Examine the data to identify patterns, risks, connections, or exposed assets. - Reporting
Present findings in a clear and actionable format to support decision-making
These steps ensure OSINT activities remain effective, ethical, and goal-oriented.
What Is the Difference Between Active and Passive OSINT Frameworks?
OSINT frameworks can be classified into passive and active approaches, depending on how information is collected.
Passive OSINT Framework
Passive OSINT involves collecting information without directly interacting with the target. This includes searching public websites, social media profiles, news articles, and public records. It is low-risk and does not alert the target.
Active OSINT Framework
Active OSINT involves limited interaction with the target, such as visiting websites or running scans that may leave traces. While still legal, it carries a higher risk of detection and must be used carefully.
Understanding the difference helps organizations choose the right OSINT framework approach based on risk level and investigation needs.
Conclusion
The OSINT framework is an essential tool for transforming publicly available information into meaningful intelligence. By following a structured methodology, organizations can identify risks, improve cybersecurity awareness, and stay ahead of potential threats.
Whether used for defense, investigations, or awareness training, an effective OSINT framework helps organizations understand their digital footprint and protect themselves in an increasingly transparent online world.







